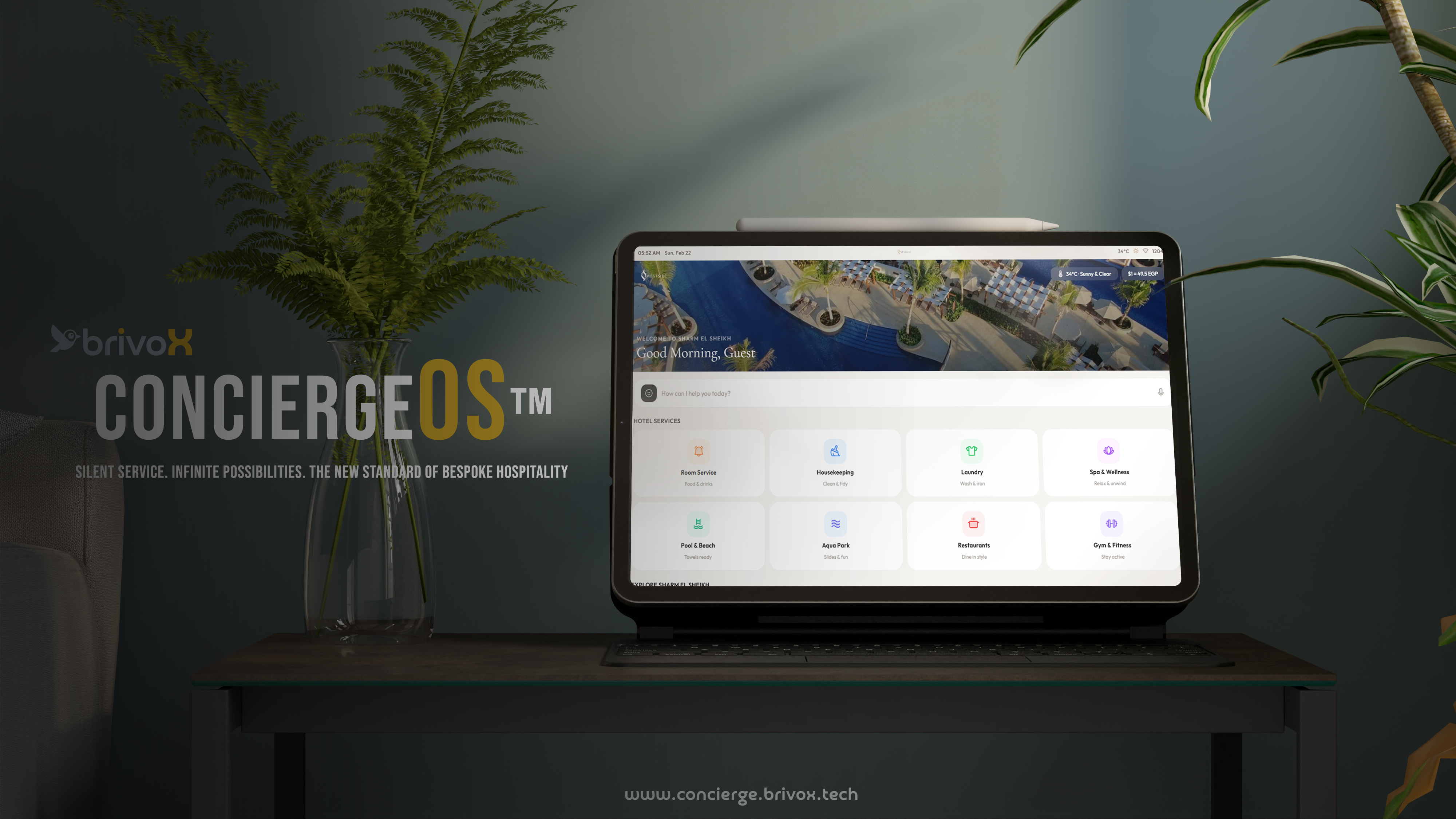
A massive, highly-secure SaaS IoT platform for Sharm El Sheikh resorts. Fully autonomous ecosystem.
Inspect platform
Bishoy Emad Raouf Fouad
I am a Lead Software Engineer, Red Teamer, and former Police Investigator (Police Academy Alumni, Class of 2017). My technical journey spans 20 years of full-stack engineering, heavily augmented by 6 years of relentless operations in Offensive Security.
As a former investigator, my psychological grip on human vulnerabilities and social engineering is unmatched. I don't merely discover flaws—I build complete exploitation environments and develop bespoke cyber arsenals. Proven by the responsible disclosure of 80+ critical vulnerabilities to global vendors and the systemic compromise of highly defended enterprise-grade network simulations, I fuse investigative supremacy with elite software architecture to effortlessly shatter web applications—and reconstruct them to be mathematically impenetrable.
Premium builds engineered with precision, massive infrastructure, and flawless UX.
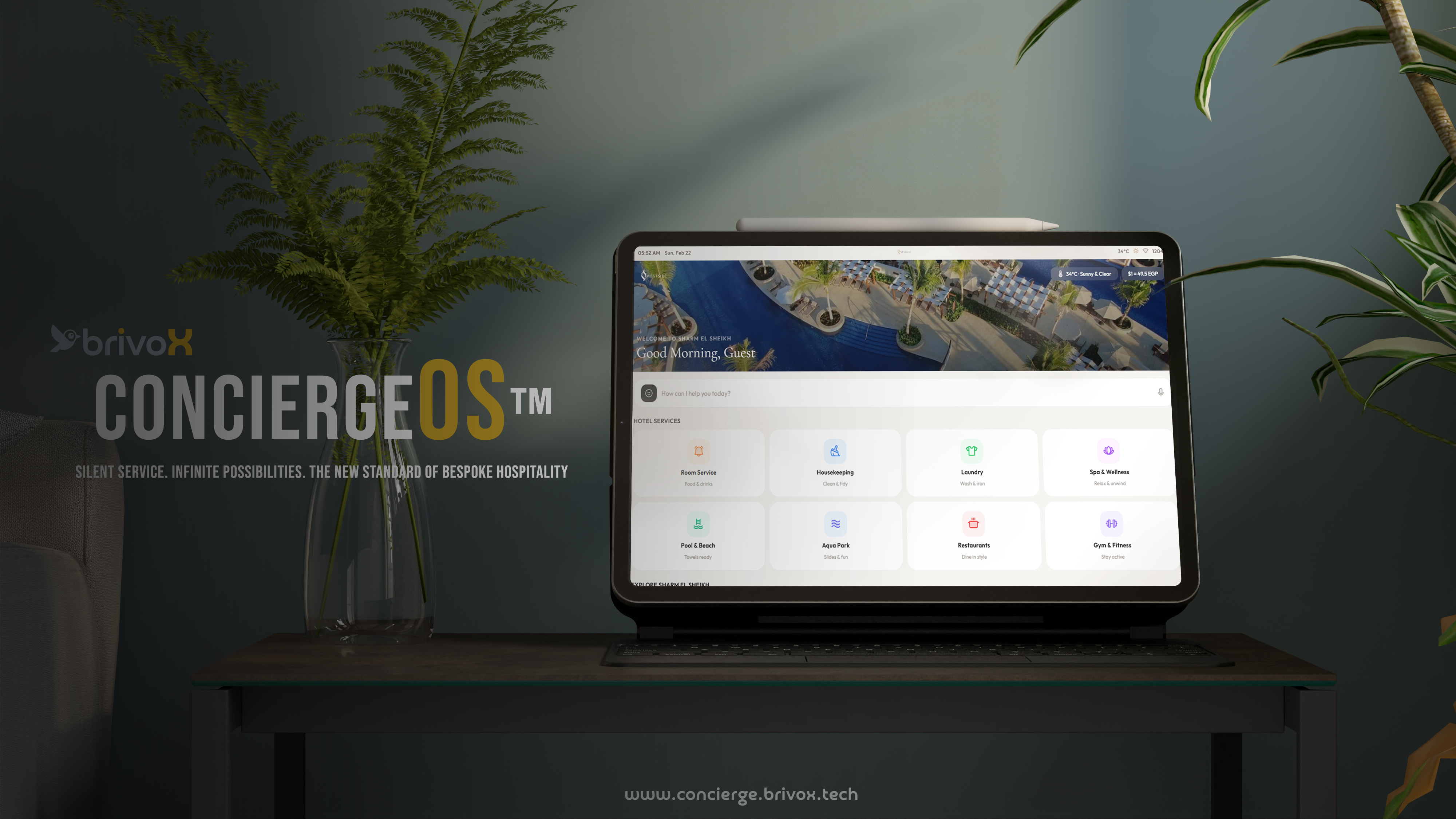
A massive, highly-secure SaaS IoT platform for Sharm El Sheikh resorts. Fully autonomous ecosystem.
Inspect platform
Ultra-fast, mobile-first booking platform. Completely decoupled front-end communicating via secured APIs.
Inspect platform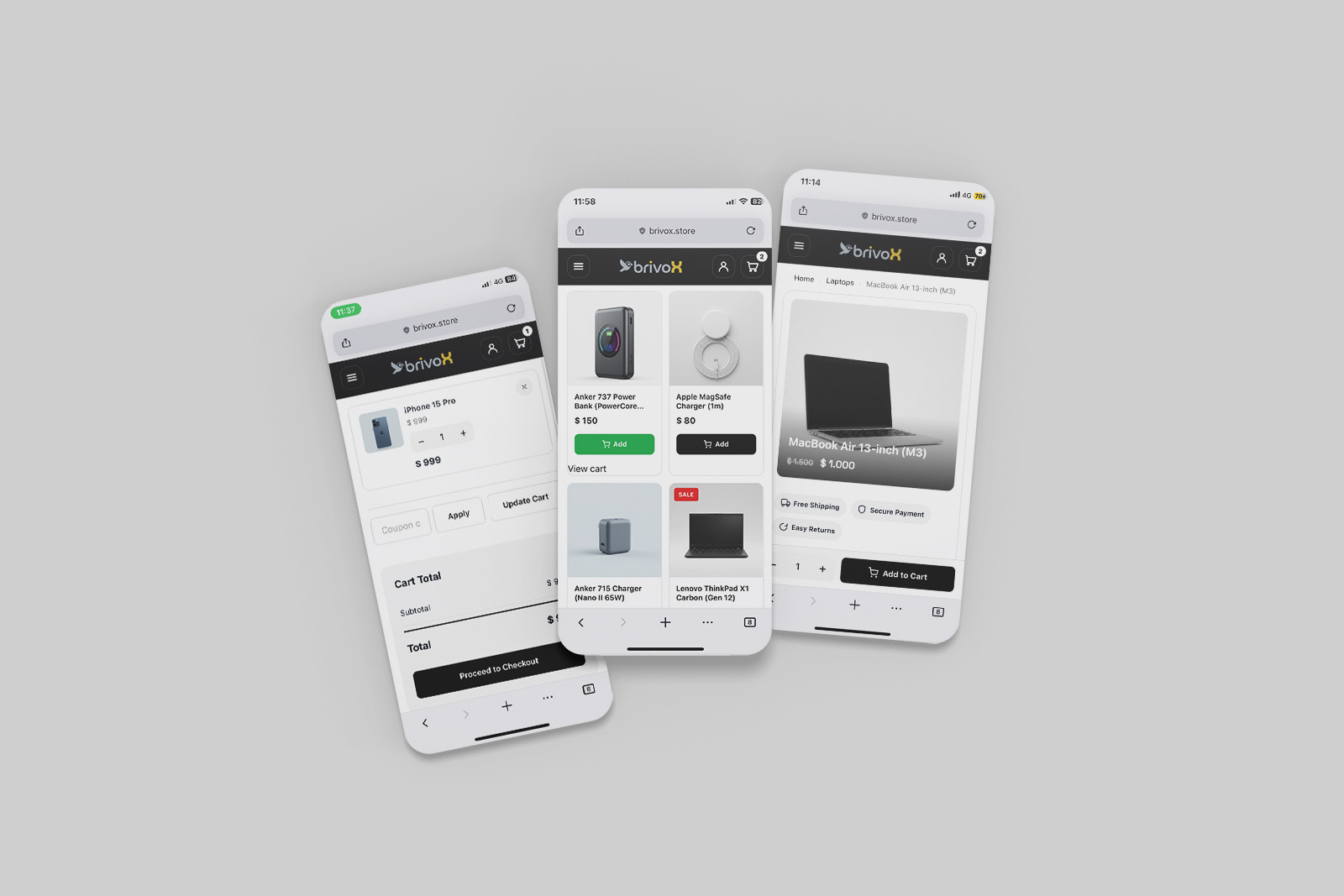
A modernized WooCommerce deployment converted to a native mobile app with extreme performance.
Inspect platform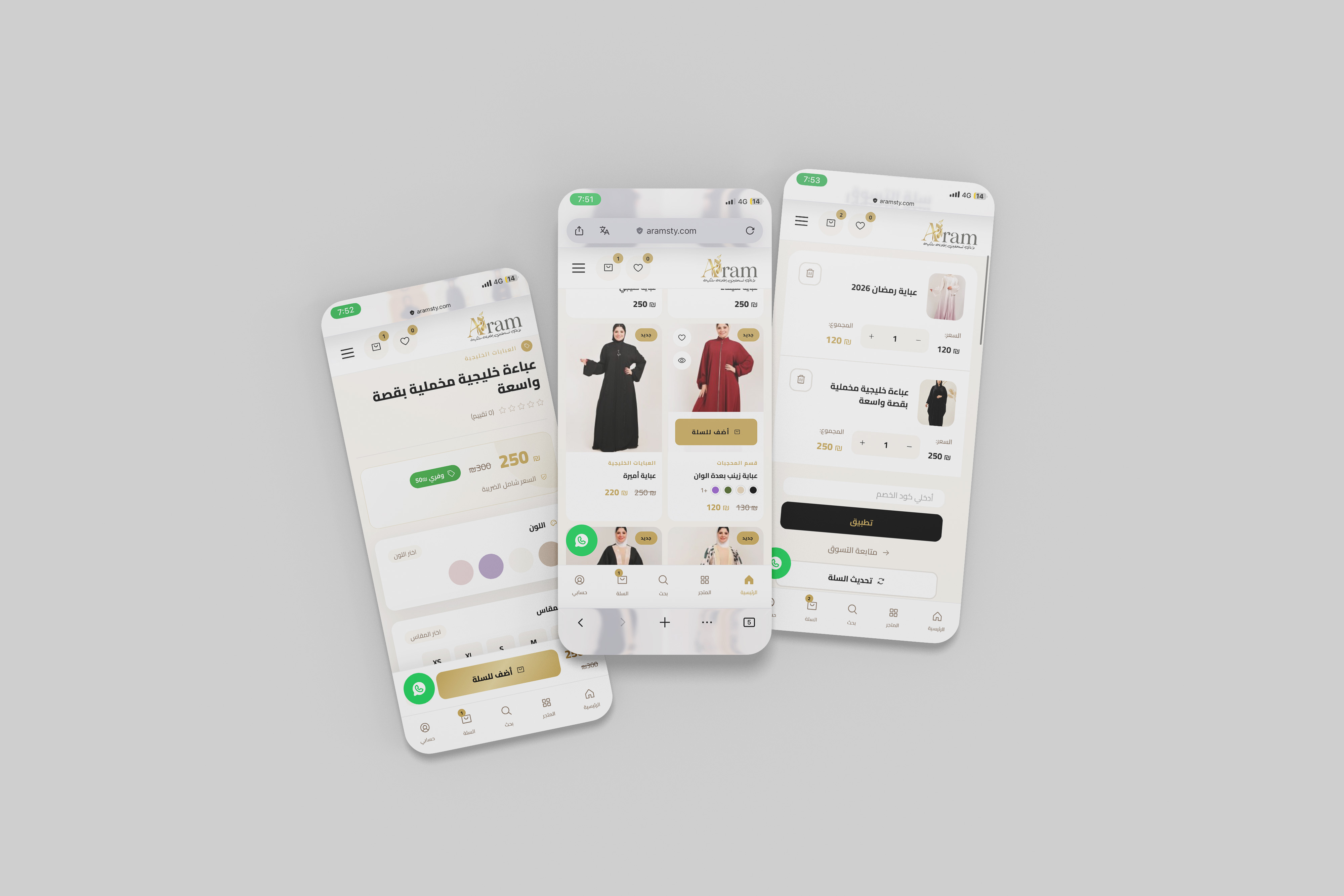
Custom core control plugin and zero-bloat theme built entirely from scratch with complex logic.
Inspect platform


